The Cyber Ireland Threat Intel Group aims to build the expertise within the Cyber Ireland community to develop Threat Intelligence capabilities through the sharing of knowledge and experiences at a strategic level.
A) Introduction Phase:
1st Session: Threat Intel and Mitre Att&ck 101
2nd Session: Developing your TI Strategy
3rd Session: Law Enforcement
4th Session: Threat intelligence platforms and consumption 101
B) Implementation Phase:
5th Session: Active Defense with Incident Response
6th Session: How to build a Threat Intel Program
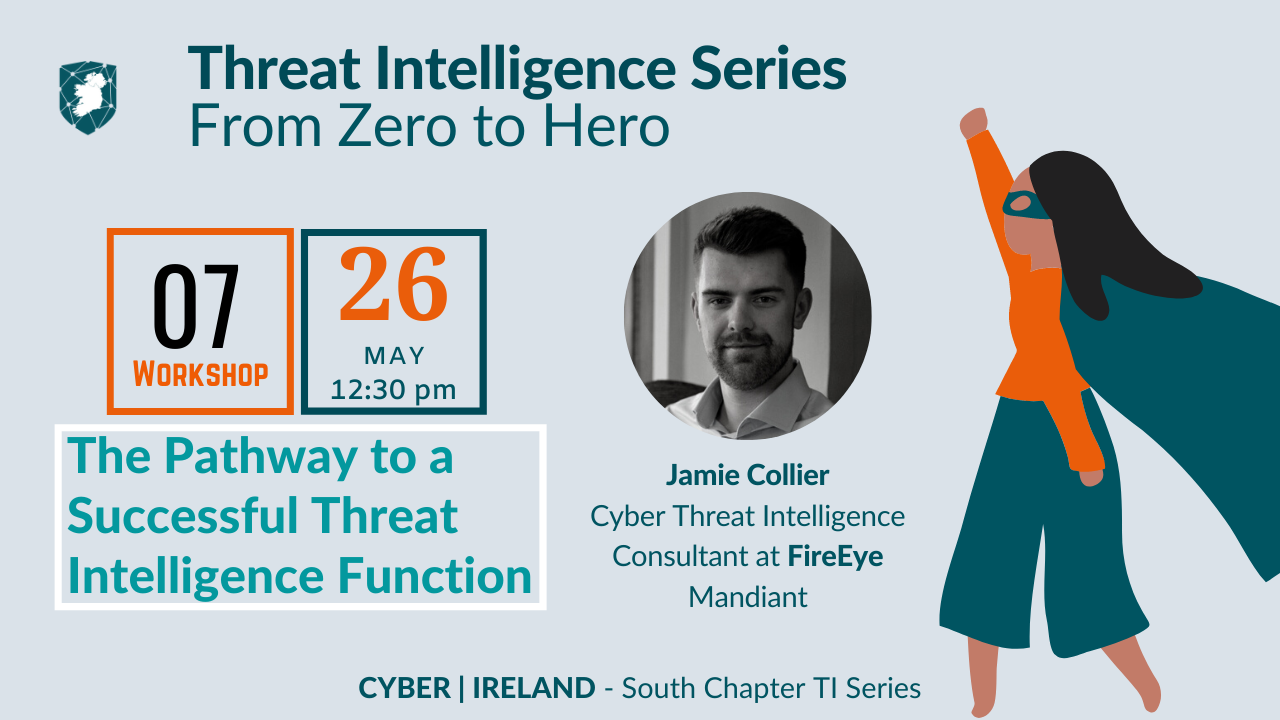
7th Session: The Pathway to a Successful Threat Intelligence Function
On the 26th May we were joined by Dr. Jamie Collier, Cyber Threat Intelligence at FireEye to talk us about The Pathway to a Successful Threat Intelligence Function.
Cyber Threat Intelligence (CTI) is never an end in itself. It instead serves a broader mission: to inform, advise, and empower stakeholders within an organization. This talk will outline how an organisation can build and develop a successful CTI function that is able to improve security outcomes and empower individuals across a security function. The talk will first outline what FireEye Mandiant considers the gold standard for CTI functions, before outlining advanced CTI use cases among various stakeholders.
You will learn:
– The critical components of any successful CTI function.
– How to shift from a reactive to proactive CTI posture.
– How to leverage MITRE ATT&CK mapping and YARA rules to improve security outcomes.
– Utilising intelligence in cyber risk.
Agenda
-
-
-
Introduction to Cyber Threat Intelligence (CTI)
- Defining Intelligence-Led
- Intelligence-Led Security
- Paradox of Choice
- Navigating Distraction
-
The Pathway to Success
- CTI Process Lifestyle
- Building for Success – The Gold Standard
- Developing a Cyber Threat Profile
- Getting to know your Stakeholders
- Building Requirements-Driven Approach
-
Shifting to a Proactive Response
- Optimizing Feedback
- From Reactive to Proactive Responses
- Ransomware Playbooks
- Leverage Playbooks
- High-Leverage Security Decision
- Intelligence/Led Red Teaming
- Vulnerability Prioritization Philosophy
-
-
About the Speaker:
Dr Jamie Collier is a Cyber Threat Intelligence Consultant at FireEye. He was previously the Cyber Threat Intelligence Team Lead at Digital Shadows and has completed a Ph.D. in cybersecurity at the University of Oxford where he remains active as a research affiliate with the Centre for Technology and Global Affairs. Jamie was previously based at MIT as a Cyber Security Fulbright Scholar and has experience working with the NATO Cooperative Cyber Defence Centre of Excellence, Oxford Analytica, and PwC India.
To watch the webinar see our Youtube channel:
Do you want to be part of Ireland’s Cyber Security Cluster?
Check our Membership Page